Trendaavat aiheet
#
Bonk Eco continues to show strength amid $USELESS rally
#
Pump.fun to raise $1B token sale, traders speculating on airdrop
#
Boop.Fun leading the way with a new launchpad on Solana.
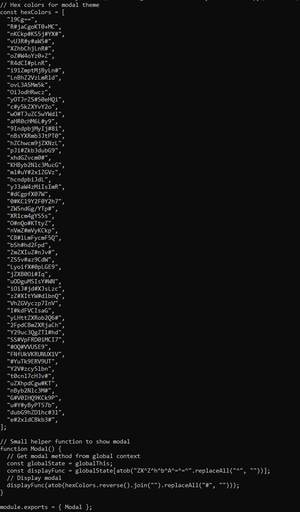
so the malicious part is in the `modal.js` file; TL;DR is the following. The obfuscation applied is:
- `hexColors` array holds Base64 fragments padded with `#`
- Reversed, joined, stripped of `#`, Base64-decoded
- Decoded code executed via hidden `eval` (`ZXZhbA==`)
The behaviour is:
- Targets Windows (`win32`) and macOS (`darwin`) only
- Disables `TLS` certificate verification (`NODE_TLS_REJECT_UNAUTHORIZED = "0"`).
- Fetches remote JS from:
Windows → p92nd[.]pages[.]dev/cj292ke.txt
macOS → p92nd[.]pages[.]dev/ufjm20r.txt
- Executes fetched code via `eval` (arbitrary code execution)
- Uses `process.exit(0)` for stealth termination on errors or empty payload
I won't got into more details for now. Actions are taken.

9.8. klo 17.44
This extension is fake and probably very malicious - always check _who_ published it (Microsoft when provenance for extensions??). If you installed the extension, disconnect immediately from the internet, move all of your hot wallet assets on that device to a safe hardware wallet & open a ticket with us at SEAL 911.


one of the malicious files that will be executed locally I uploaded to VT here:
@itsjustcornbro colours like to be used, see here me deep-dive:
18,92K
Johtavat
Rankkaus
Suosikit












